What is CTF (Capture The Flag) ?
Capture the Flag (CTF) is a competition that related to information security where the participants will be test on a various of security challenges like web penetration testing, reverse engineering, cryptography, steganography, pwn and few others more. Participants must get the “flag” to gain their points. So, the team who have the highest point at the end of the game will be the winner.
Usually, CTF competition is free and most of CTF out there are online and organized by various organizer. In malaysia we have wargames my where it is a 24-hours online CTF hacking game. It’s open to all Malaysians – students, academics, professionals, hobbyist or anyone. The organizer not just a big company, but also the organizer may from various local universities.

Here a video by LiveOverflow (a hacking and hardcore CTF player) youtube channel on Capture The Flag Competition:
Why participate in CTF?
There are few reasons why you must join CTF competition: –
- To gain knowledge and experience in Cyber Security environment.
- Hobby
- Socializing and networking
- To make your resume awesome!
Sometimes, when you participate on CTF, the industry will acknowledge your skill and maybe you will be recruited as one of their staff.

Types of CTF
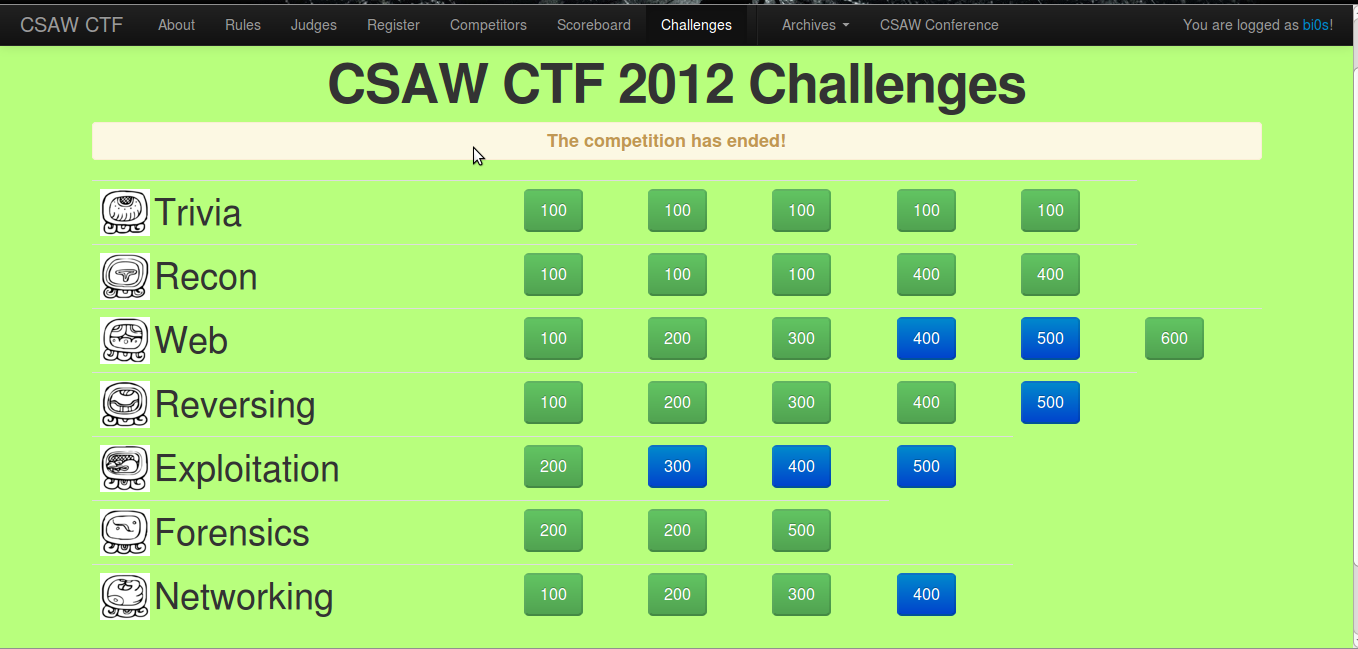
There are three common types of CTFs: Jeopardy, Attack-Defence and mixed.
- Jeopardy-style CTF
Jeopardy-style usually have multiple categories of challenges, which contains a variety of questions of different point values and difficulties. - Attack-defence CTF
While on this type of CTF competition, each team is given a task to defend their network or server and the other will attack the opponents. Teams may attempting to take an opponent’s flag from their machine by pwn(own) the opponent’s machine.
Usually the flags that organizer give are easily recognizable strings, like “FLAG{th1s1s7h3fl4g}” so that participants don’t miss them.

Categories of challenge in Jeopardy-style CTF
In such competitions there usually are different categories of challenges and within each category, challenges are sorted by their difficulty.
Traditional categories include:
- Web: This type of challenges focus on finding and exploiting the vulnerabilities in web application. The may be testing the participants’ knowledge on SQL Injection, XSS (Cross Site Scripting), and many more.
- Forensics: Participants need to investigate some sort of data, like do a packet analysis on .pcap file, memory dump analysis and so on.
- Cryptography: Challenges will be focus on decrypting a encrypted strings from various type of cryptography such as Subtitution crypto, Caesar cipher and many more.
- Reversing (or Reverse Engineering): RE usually need participants to explore a given binary file weather PE file, ELF file, APK or some types of other executable binary. Participant need to find the key by decompilation, disassemble using static or dynamic analysis or other reverse engineering tools.
- Exploitation: Within this type, the goal is to build an exploit, very often for a binary, though sometimes for a Web application. Almost always contestants have (explicit) access to the source code of the application, unlike the Reversing category, where a big part of the challenge is that you have to essentially play “in the dark”.
- Miscellaneous: Everything not listed else that is still relevant to Information Security is in this category. This need require Google-Fu skill.
Skill required in CTF
- Google-Fu Skill
Sometimes, flag and details information for your findings during solve the challenges can be get by just google the title, description and related information. Miscellaneous category require google skill. If you don’t know anything about the challenge just google the keywords. Sometimes if you know little bit of information and concept about the challenges, just google the concept + “write-ups”. Usually, organizer make challenge based on CTF online platform. - Learn python or other scripting languages.
Programming such as python will make us easier to do what we looking for. Sometimes, challenges require scripting knowledge and skill to generate/get our flag. - Linux skill
There is a lot of good tools in Linux that you can use for solving CTF challenges. Hacker out there in real-world prefer Linux than using Windows. These some tools and command line I list for you to explore;- cat
- nc
- strings
- file
- grep
- unzip
- nano, vim – text editor
- chmod
- binwalk – Stegano, Forensics
- pdfcrack – crack pdf password
- Exiftool – Stegano, Forensics
- foremost – Stegano, Forensics
- base64 – Crypto
- gdb – Reverse Engineering
- ltrace, strace – Reverse Engineering
- and many more!
- Web Penetration Skills
CTF, often have challenge for web hacking. Knowledge in web concept and pentest is so much important for participant to solve the challenge. Usually, the challenges are based on OWASP Top 10. Exploring the OWASP top 10 will get you some good skill for this. Refer this https://www.greycampus.com/blog/information-security/owasp-top-vulnerabilities-in-web-applications. - Reverse Engineering Skills
RE required knowledge of understanding the codes. You need to have a strong C programming languages and Assembly language for this. If you want to explore more, read this book https://github.com/harryskon/re4b. - Pwn Skills
In order to master pwn you need have RE skills first. Pwn is a leetspeak slang term derived from the verb own, meaning to appropriate or to conquer to gain ownership. Tools like pwntools will help you a lot in CTF. Refer this https://dhavalkapil.com/blogs/Buffer-Overflow-Exploit/. - Wireshark and Network Miner tools.
Mastering PCAP analysis will make us good in CTF. CTF often too have challenge about pcap analysis. Just youtube the tutorial how to use Wireshark. Strings and binwalk command sometimes can help you. - Cryptography
Use online tools to decrypt. Google some information.
Tips for CTF
Steganography

Note:
- Usually when organizer gave us Image, M usic, Video, Zip, EXE, File System, PDF and other files, it a steganography or forensics challenge.
- Always issuing file <filename> command to whatever file you get first!
- Checkout the EXIF data of the file by using exiftool <filename> command.
- Try file carve using foremost <filename> command. Foremost support all files.
- Note the flag at one text file.
-
Image @ photo
- Use strings command to that file.
- Google the images, differentiate the md5hash
- Try grep -i something from the strings command output.
- Try also cat command and grep -i it!
- Checkout the EXIF data of the file by using exiftool <filename> command.
- Analyse the header and the content of the file using HxD.
- Know the file signature. Maybe they gave us corrupt header! So fix it!
- Maybe zoom-in and zoom-out method can get the flag.
- Use https://www.tineye.com/ to reverse search the image in the internet.
- Rename the image file to archive file format, and unzip or unrar it.
- Use imagemagick command tool to do image manipulation.
- Use photoshop software to edit it.
- Use sng commmand for png file format. It is a decompiler for Scriptable Network Graphics.
- Use Stegsolve.jar tools.
- File carve using binwalk -e command.
- File carve using foremost <filename> command.
- File carve using steghide –extract -sf <filename>. Try find the password with ownself.
- Check for any corruption on PNG file by using pngcheck <filename.png> command.
- Try manipulate the png files by issuing zsteg -a <filename.png> .
- Use SmartDeblur software to fix blurry on image.
- Use stegcracker <filename> <wordlist> tools Steganography brute-force password utility to uncover hidden data inside files.
- Use tesseract to scan text in image and convert it to .txt file.
- Use SilentEye.
-
Some of online stegano decoder :-
- https://futureboy.us/stegano/decinput.html
- http://stylesuxx.github.io/steganography/
- https://www.mobilefish.com/services/steganography/steganography.php
- https://osric.com/chris/steganography/decode.html
- https://incoherency.co.uk/image-steganography/
- https://manytools.org/hacker-tools/steganography-encode-text-into-image/
- https://www.geocachingtoolbox.com/index.php?lang=en&page=steganography
- https://steganosaur.us/dissertation/tools/image
-
Zip
- File carve using foremost <filename> command.
- Unzip it.
- Use zipdetails -v command to display details about the internal structure of a Zip file.
- Use zipinfo command to know details info about Zip file.
- Use zip -FF input.zip -out output.zip attempt to repair a corrupted zip file.
- Bruteforce the zip password using fcrackzip -D -u -p rockyou.txt filename.zip
- Binwalk it.
-
Music file
- Use Audacity.
- Use Sonic Visualizer. Look at spectogram and other few Pane.
- Use Deepsound.
- Use SilentEye.
- Some of online stegano decoder for music:-
-
Text
- Use http://www.spammimic.com/ that can decode hide message in spam text.
-
PDF
-
Lot of tools in kali linux for pdf
- pdftotext <filename.pdf>
- peepdf <filename.pdf>
- pdfimages <filename.pdf>
- pdfcrack
- OfficeMalScanner.exe <filename.pdf>
- Malzilla
- PDFStreamDumper.exe
-
Lot of tools in kali linux for pdf
PCAP Analysis

Note:
- So, usually they gave us file in .pcap or .pcapng file type.
-
Note the flag at one text file.
- Use strings command the pcap file.
-
Analyse it using Wireshark.
- follow tcp streams
- protocol
- export data
- expert info
- filter
- osi layer
- find by string
- conversation
- https://hackertarget.com/wireshark-tutorial-and-cheat-sheet/
- Analyse it using NetworkMiner. It used as a passive network sniffer/packet capturing tool in order to detect operating systems, sessions, hostnames, open ports etc …
- Use binwalk
- Upload it to https://www.packettotal.com/
- Try aircrack-ng <pcap> -w <wordlist> or to crack wifi password.
- Then airdecap-ng -p <password> <pcap> it.
- Use netcat command when you find ip on it.
- Open the server ip in web browser.
- Use http://pcapng.com/ to convert pcapng file to pcap file. And analyse it using Network Miner software.
Cryptography
Whatever happen, google is your friend.
- Usually they gave us a jumbled text that we cannot understand.
- Decrypt it using online tools. Look at my bookmark bar security/online tools.
- Try and guess.
Pwn
Note:
- Usually they gave us a binary and a source code of the binary.
- Whenever you get a file, issuing file command first to it to know what really file is it.
- You need know about Assembly Language, computer architecture, C programming and Python language to make script for this challenge!
- Note the flag at one text file.
- Do some reverse engineering first.
- Understand the C code.
- Use Zeratools.
- Maybe overflow concept.
- Use pwndbg.
- Use strings <filename> command to read the strings in the binary.
- Maybe some grep -i command too.
- Use DIE on the binary.
- Use ltrace ./<filename> command to know what library function are being called in the binary.
- Use strace ./<filename> command to know what system and signal function are being called in the binary.
- Use nm <filename> command to know what symbol being called in the binary.
- Use readelf -a <filename> command. It will displays information about ELF files.
- Use IDA Pro software to perform static analysis on the binary.
- Use Snowman software to perform decompiler.
- Use debugger like GDB-Debugger to debug the binary.
- File traversing on the netcat. Like ../flag
- Use pwntools to do script exploitation.
- Use cyclic to create pattern
-
Gdbpeda pwn
- Breakpoint at strcmp
- pattern create [number of pattern]
- x/s $[register/stack/base]
- pattern offset [strings of pattern]
- Then you get the value to pwn it.
- gdbs [./binaryname] to switch between peda and pwndbg
- Use python like example, python -c “print ‘A’*28 + ‘\x39\x05′” | ./<filename>
Reverse Engineering
Notes:
- Whenever you get a file, issuing file command first to it to know what really file is it.
- Checkout the EXIF data of the file by using exiftool <filename> command.
- Use strings <filename> command to read the strings in the binary.
- Maybe some grep -i command too.
- You need know about Assembly Language and computer architecture for this challenge!
- Note the flag at one text file.
Usually they gave a binary file. Weather it
- PE file
- ELF File
- APK File
- .NET File
- Java file.
- Python File
-
PE File
- Use strings <filename> command to read the strings in the binary.
- Maybe some grep -i command too.
- Use DIE, PEID, PEBear, or PEView software to do static file analysis. Find details of file in there!
- Use HxD to check the header file, file signature. Maybe the corrupt file sign one.
- Find it whether it packed or not. Find online unpack.
- Find it whether the binary has anti-debug or not.
- Use IDA Pro software to perform static analysis on the binary.
- When do analysis static or dynamic focus on strcmp, function call, conditional jump.
- Use Snowman software to perform decompiler.
-
Use debugger like Immunity Debugger, x64Dbg/x32Dbg, or WinDbg to debug the binary.
- Modify and assemble the binary. Like change PUSH 0 to JMP <flag address>.
- Modify conditional JUMP.
- After doing some modifying stuff..
- right-click -> copy -> select all -> right click again -> copy to executable -> all modifications -> click copy all -> right click again -> save file -> rename it -> open back
- or in x64dbg just click patch.
- Scan the binary on virustotal.com to know something malicious.
- run command rundll32 <dllfilename>
- Use eXeScope to find out about header, import and resource of the binary.
- Use universal extractor to extract files in the binary.
- Buat script balik lepas tgk code decompiler
-
ELF File
- Use strings <filename> command to read the strings in the binary.
- Maybe some grep -i command too.
- Use DIE on the binary.
- Find it whether it packed or not. Find online unpack.
- Find it whether the binary has anti-debug or not.
- Use HxD to check the header file, file signature. Maybe the corrupt file sign one.
- Use ltrace ./<filename> command to know what library function are being called in the binary.
- Use strace ./<filename> command to know what system and signal function are being called in the binary.
- Use nm <filename> command to know what symbol being called in the binary.
- Use readelf -a <filename> command. It will displays information about ELF files.
- Use IDA Pro software to perform static analysis on the binary.
- Use Snowman software to perform decompiler.
- Use debugger like GDB-Debugger to debug the binary.
-
APK File
- Use APKTool <filename> command tools.
- Use Android Emulator to run the program.
- Use Android Debug Bridge.
- Use dex2jar <filename> command tools.
- Use jd-gui.
- rename the file to zip file. Unzip it.
- apktool -> file extracted -> use dex2jar to convert .dex file to .jar file-> open tha .jar file using jd-gui
-
.NET File
- Use dnSpy software. Very powerful. Edit it -> compile -> save all. Try run the program back!
-
Java file
- Use Java Decompiler program to decompile it.
-
Python File
- Use Easy Python Decompiler to decompile it.
Web exploitation

Note:
- Usually they gave us web link or IP of the URL.
- This challenge require knowledge about web penetration concept.
- Refer https://jdow.io/blog/2018/03/18/web-application-penetration-testing-methodology/ for more details.
- https://highon.coffee/blog/lfi-cheat-sheet/
- https://www.aptive.co.uk/blog/local-file-inclusion-lfi-testing/
- https://www.netsparker.com/blog/web-security/sql-injection-cheat-sheet/
- https://highon.coffee/blog/penetration-testing-tools-cheat-sheet/
- Note the flag at one text file.
- View the page source first. Analyse it!
- Save page as to look to full code of JS.
- Use Inspect Element tools.
- Try php console alert(function) or console.log(function) on function that suspicious.
- Try to look to <web URL>/robots.txt
- Use nmap <URL> command to look up for the open port.
- Use DirBuster tools to try directory traversing.
- Use WPScan if the web is using WordPress platform.
-
Focus on Cookies that the web use.
- if the cookies false, make it true.
- Focus on User Agent that the web use.
- Use Burpsuite or Fiddler software to intercept request.
- Try execute some Linux/Windows command at textbox in the web.
- Try upload php shell on file uploader. For file uploader vulnerability.
- Look for index.php for the web.
- Use /../../../ for file traversing.
- Try to find /etc/passwd of the web.
- OWASP Top 10.
- Use URL injection.
- Use URL Trick like modify the parameter.
- Use SQL Injection.
- Use Cross-Site-Scripting method.
- Local File Inclusion.
- Remote File Inclusion.
- Use SQL and XSS sidebar
- Look for backup file like index.php.bak.
- XSSer – Automated XSS testor. Of course, command line.
Trivia Challenge
- Google is your friend. Use quote mark.
- Maybe the source code of CTF platform.
- Reverse image.
- File traversing on CTF platform.
Tools in CTF

- https://github.com/zardus/ctf-tools
- https://github.com/MrMugiwara/CTF-Tools
- https://github.com/apsdehal/awesome-ctf
There are many online CTF / Hacking websites out there that you can train yourself and improve your knowledge in infosec world.
Here some of them that I got by some google-fu and also from variety of other sources.
List of Hacking & CTF Challenge Sites
General CTF
- https://www.net-force.nl/challenges/
- https://ctfs.me/
- http://www.wechall.net/challs
- http://www.mod-x.co.uk/main.php
- https://www.root-me.org/?lang=en
- https://picoctf.com/
- http://hax.tor.hu/welcome/
- https://ringzer0team.com/home
- https://backdoor.sdslabs.co/
- http://shell-storm.org/repo/CTF/
- https://w3challs.com/
- https://ctflearn.com/
- https://ctf365.com/
- https://www.hellboundhackers.org/
- https://www.hackthis.co.uk/
- https://www.enigmagroup.org/
- http://ctf.komodosec.com/index.php
- http://bright-shadows.net/
- https://ctf101.org/
- https://hackcenter.com
- https://www.hackthissite.org/
- https://www.rankk.org/
- https://canhack.me/
- https://hackburger.ee/challenge/
- https://www.hackergateway.com/
- https://www.wixxerd.com/challenges/
- https://www.sabrefilms.co.uk/revolutionelite/
- https://www.challengeland.co/#
- https://ctf.hackerfire.com/
- http://ctf.infosecinstitute.com/index.php
Web Exploitation
- https://hack.me/s/
- http://www.gameofhacks.com/
- https://join.eset.com/en/challenges
- http://www.dvwa.co.uk/
- http://google-gruyere.appspot.com/
- http://www.hackertest.net/
- http://solveme.peng.kr/
- http://www.hacking-challenges.de/
- https://redtiger.labs.overthewire.org/
- https://www.hackthebox.eu/
Reverse Engineering
- https://microcorruption.com/
- http://reversing.kr/challenge.php
- https://www.malwaretech.com/beginner-malware-reversing-challenges
- https://crackmes.one/
- https://challenges.re/
- https://reverse.put.as/crackmes/
- https://join.eset.com/en/challenges
- http://flare-on.com/
- https://ropemporium.com/
Pwn
- http://pwnadventure.com/
- https://exploit-exercises.com/
- http://pwnable.kr/play.php
- https://pwnable.tw/challenge/
- https://www.pentestpractice.com/
Wargames
- http://io.netgarage.org/
- http://smashthestack.org/wargames.html
- http://overthewire.org/wargames/
- https://chall.stypr.com/
- http://www.underthewire.tech/wargames.htm
Cryptography
- http://cryptopals.com/
- https://id0-rsa.pub/
- http://www.caesum.com/game/
- https://www.trytodecrypt.com/index.php
- https://www.cryptoclub.org/challenges/index.php
Network Forensics
Feel free to leave your comment and give suggestion for this list.
Testimony of students from Degree in Network Technology FSTM KUIS;
Students in this program also actively involved with national Hacking competitions such as in Battle of Hackers, CRAC2018 and so forth.
Being the champions and 1st runner-up on several ocasions as in UNIKL, APU, UNITEN , Mersing Politechnic they made us proud. Hopefully they will be the first-line of defence for Malaysia cyber-terrorists.



KUIS also offer academic program for Degree in Networking Technology. Find out more here in order to learn the platform of hacking;
http://www.kuis.edu.my/en/bachelor-of-information-technology-networking-technology-hons